VPNs have shifted from niche security tools to mainstream apps promising privacy, freedom, and protection. But in 2026, the real question isn’t what a VPN does—it’s when it actually makes sense to use one. As built-in security features improve across devices and networks, VPNs are no longer essential by default. They’re situational tools, and understanding those situations is what matters.
At a basic level, a VPN encrypts your internet traffic and routes it through a remote server. In simple terms, it hides where you’re connecting from and makes your data harder to intercept. That’s especially relevant on unsecured networks, where your information might otherwise be exposed.
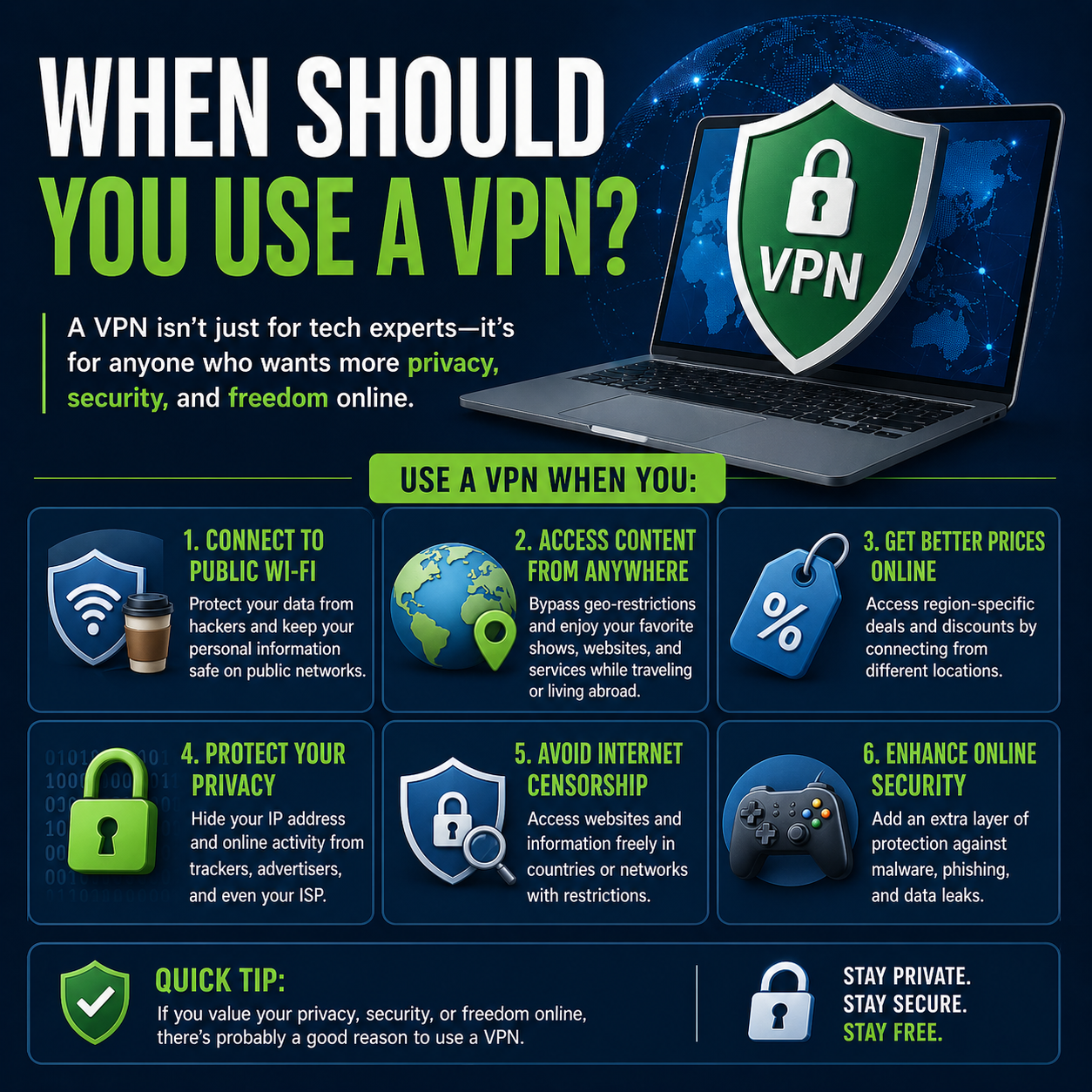
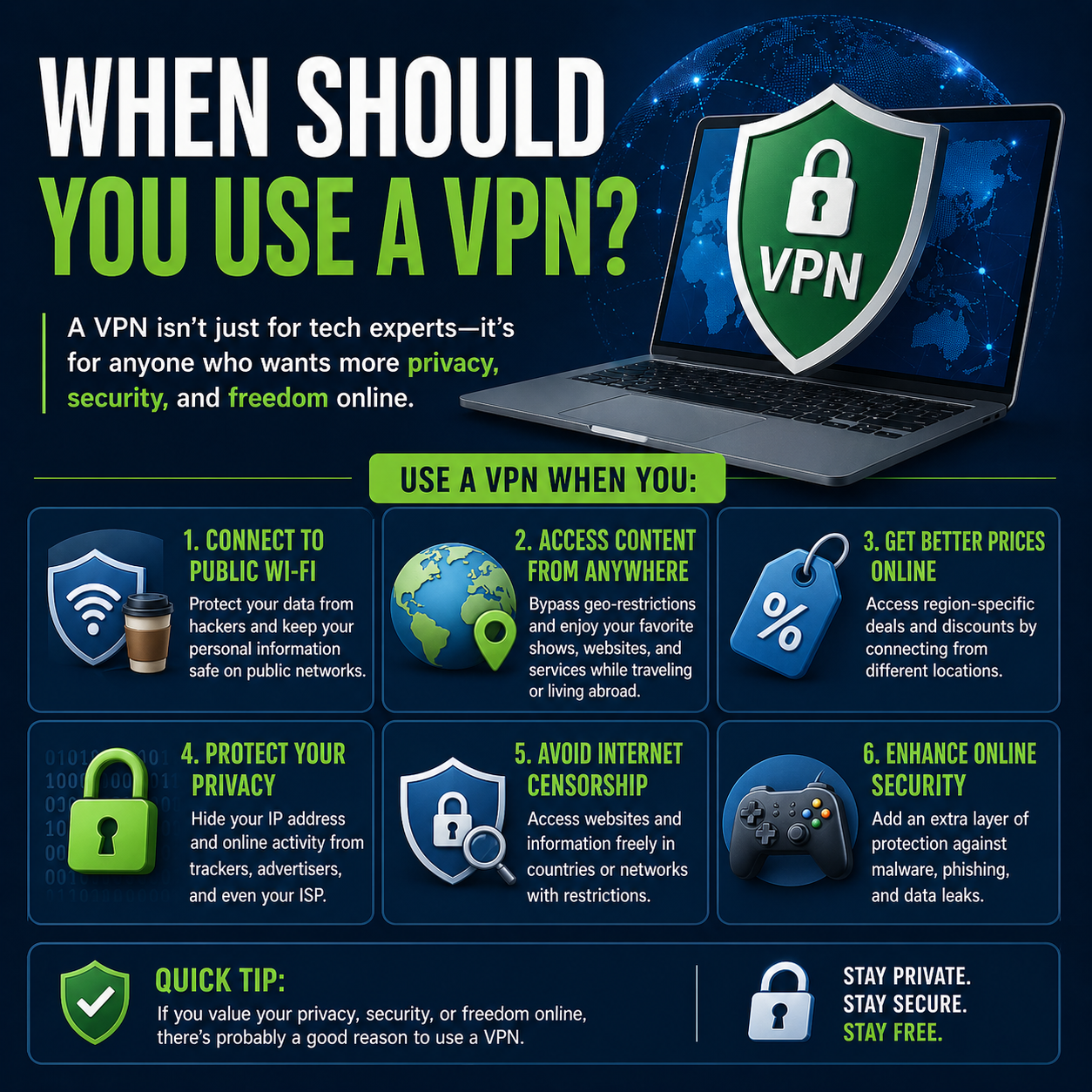
Public Wi-Fi is still the clearest use case.
Airports, hotels, and cafés often rely on shared networks with uneven security. Even though most websites now use HTTPS, a VPN adds an extra layer by encrypting all traffic—not just what happens in your browser. Compared to relying solely on browser-based protections, a VPN offers broader coverage across apps and services.
For remote work, VPNs remain a standard tool. Many companies require them to access internal systems securely, ensuring that sensitive data stays protected outside office networks. In this context, VPNs aren’t optional—they’re part of the infrastructure.
Privacy is where things get more nuanced.
A VPN can hide your browsing activity from your internet service provider and mask your IP address from websites. That sounds compelling, but alternatives have emerged. Features like encrypted DNS, tracker blockers, and private browsing modes reduce data exposure without rerouting your entire connection. Compared to these tools, a VPN offers more comprehensive privacy—but also introduces more complexity and potential slowdowns.
And speed matters.
Because a VPN routes your traffic through another server, it can increase latency and reduce download speeds. Modern protocols like WireGuard have narrowed the gap, but for gaming, streaming in high resolution, or real-time applications, the difference is still noticeable. In contrast, built-in privacy tools typically have little to no performance impact.
Streaming is a mixed case.
VPNs are often used to access content from different regions, but major platforms have become more effective at detecting and blocking them. While some premium services still work intermittently, it’s no longer a reliable solution. For most users, regional content access is now inconsistent at best.
There’s also the question of trust.
Using a VPN shifts your data from your ISP to a VPN provider. Reputable services claim strict no-logs policies, but users still need to trust that those claims are accurate. By comparison, tools built into operating systems or browsers distribute data handling across multiple entities, which can reduce reliance on a single provider.
So when should you actually use a VPN?
Use it on public Wi-Fi, when handling sensitive work remotely, or when you need to bypass network restrictions. In these cases, the added layer of encryption and location masking provides clear, practical benefits. For everyday browsing at home, however, the advantages are less pronounced, especially with modern security standards already in place.
Conclusion: In 2026, a VPN is best viewed as a targeted tool rather than a constant necessity. It’s highly effective in specific scenarios—public networks, secure remote access, and restricted environments—but less critical for routine use on secure, modern systems. Knowing when to turn it on is what ultimately determines its value.